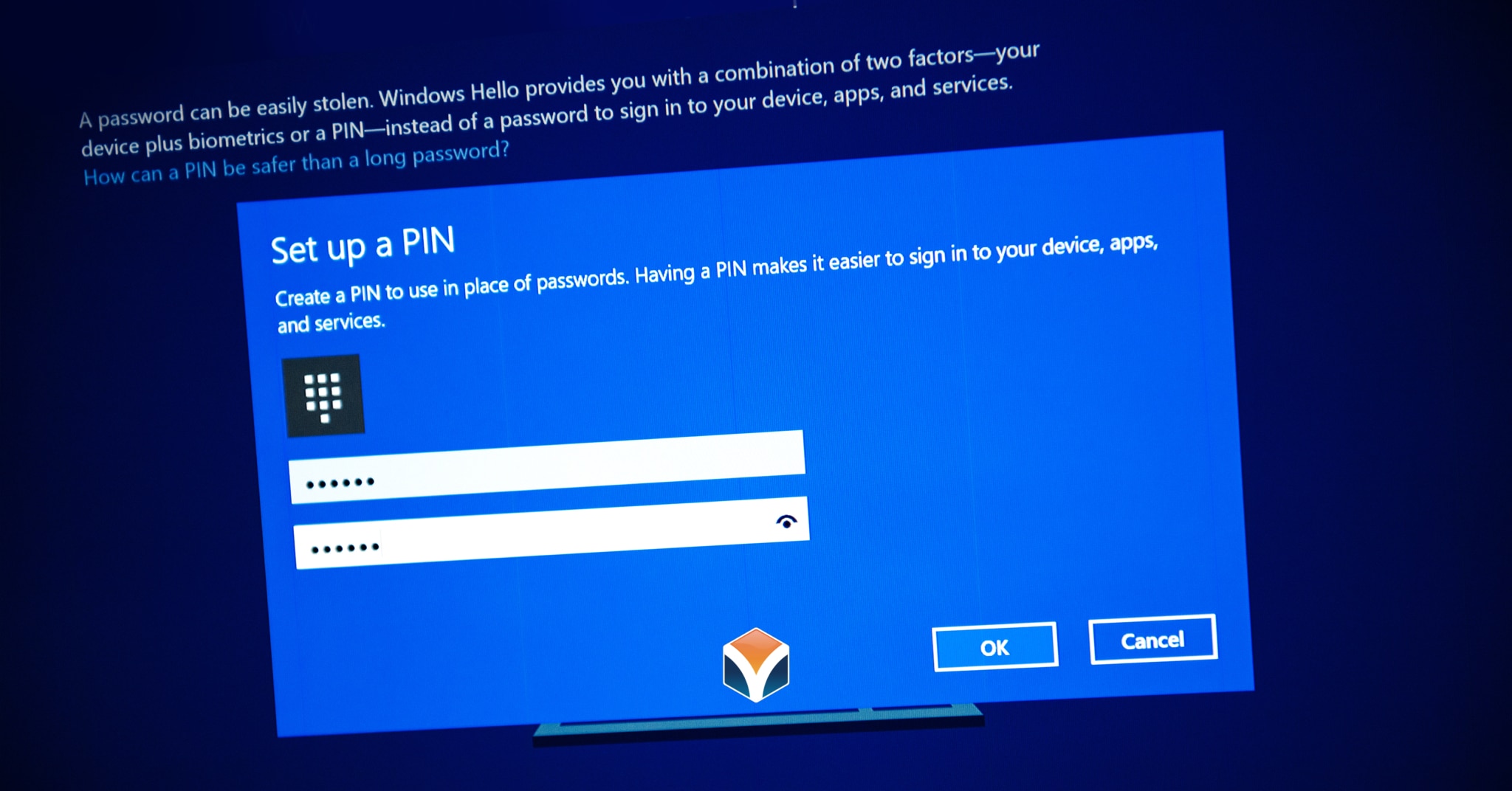
Breaking Windows Passwords: LM, NTLM, DCC and Windows Hello PIN Compared | Elcomsoft | LOGON Software Asia

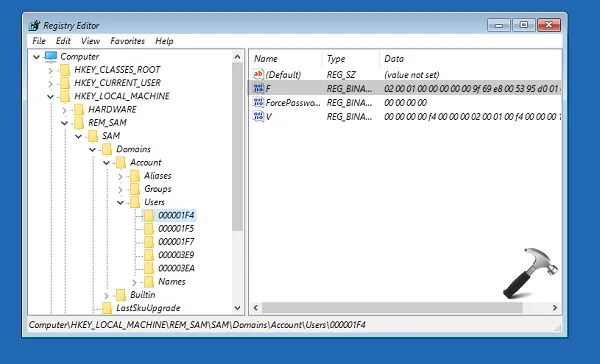
Breaking Windows Passwords: LM, NTLM, DCC and Windows Hello PIN Compared | Elcomsoft | LOGON Software Asia
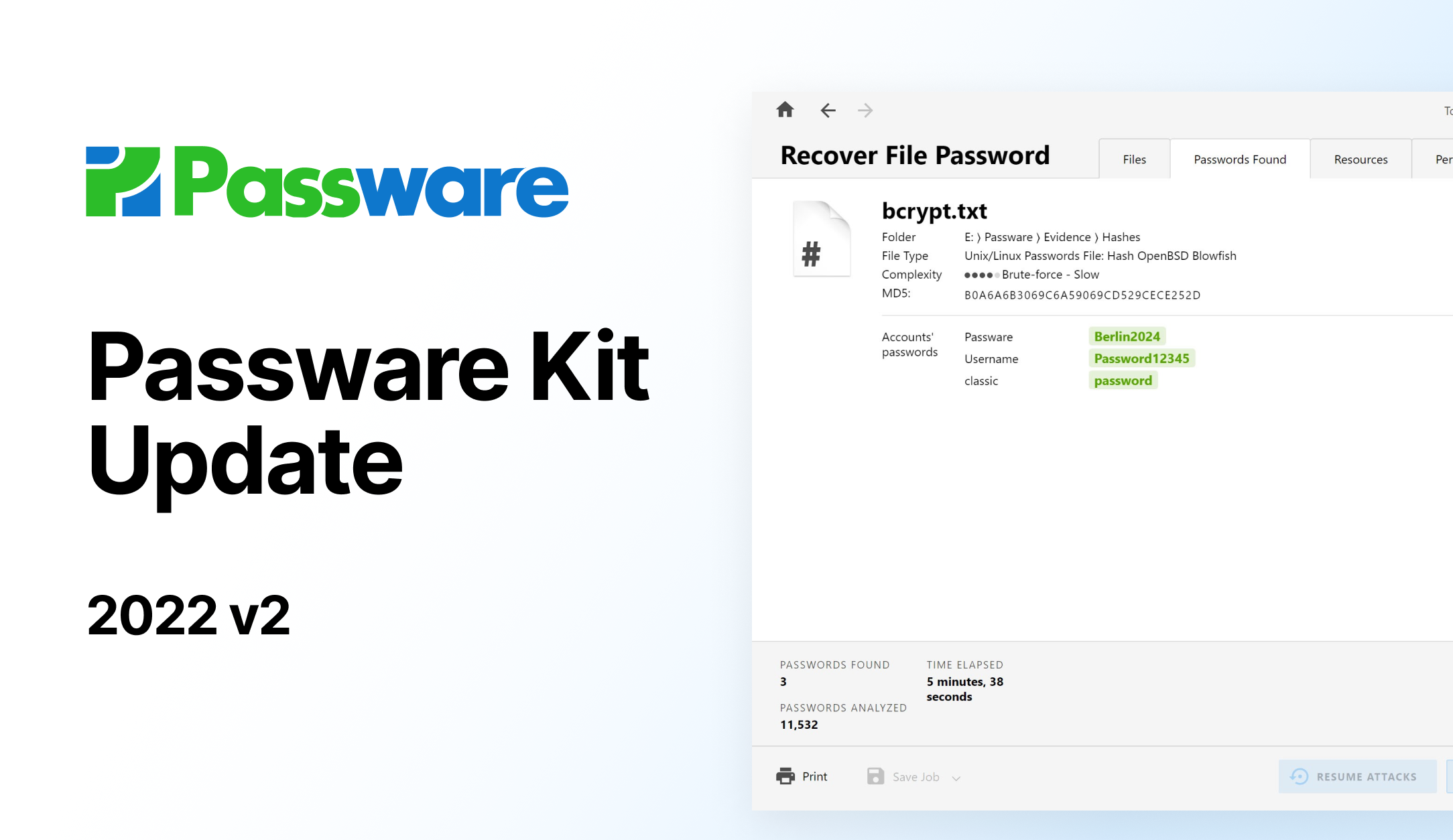
Passware Kit 2022 v2 – Password Recovery for bcrypt Hashes and OpenCL Acceleration on macOS - Forensic Focus